New to Climate Change?
Hydrogen
Hydrogen is the lightest chemical element and the most abundant chemical substance in the universe. Using fossil fuels or clean electricity, we can produce hydrogen gas, which can be stored, transported, and burned to provide power. Unlike most fuels, hydrogen does not produce the greenhouse gas carbon dioxide (CO2) when burned: instead, it yields water. This means that burning hydrogen fuel does not contribute to climate change.
The versatility of hydrogen fuel creates many opportunities to replace fossil fuels in different parts of our economy. It can provide long-term energy storage for the electric power sector, fuel for heavy duty transportation, and heat for industrial processes requiring high temperatures, like steel or concrete production. Today, hydrogen is mainly used in the petrochemical, food processing, and fertilizer industries, and in cars with hydrogen fuel cells. Countries such as Japan are exploring its use in public transportation.
For the climate, not all hydrogen is created equal
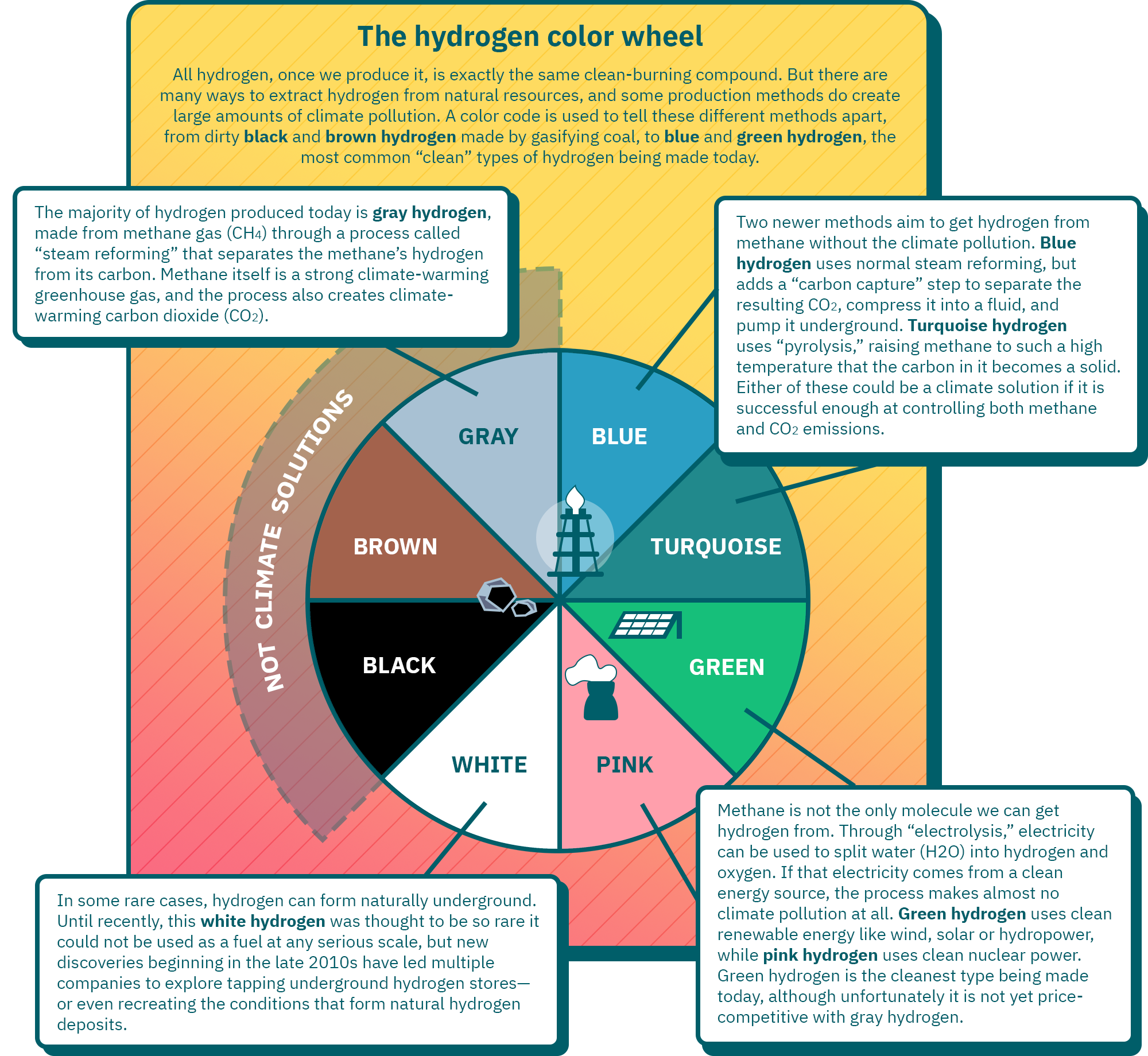
Because pure hydrogen is so rare on Earth, the hydrogen we use must be produced from other compounds. However, hydrogen production can have a large environmental impact depending on how it is produced. Today, close to 95 percent of hydrogen production is from fossil fuels like natural gas and coal. As a result, we emit 920 million tonnes of CO2 each year to produce 97 million tonnes of hydrogen.1
A wide range of processes can be used to produce hydrogen, including:
- thermochemical processes like “reforming” natural gas or coal or “gasifying” biomass;
- electrolytic processes that split water into hydrogen and oxygen using electricity;
- photolytic processes that split water into hydrogen and oxygen using sunlight;
- biological processes using algae or bacteria.
Among these options, there are two ways to move toward cleaner hydrogen production that are cheap enough to pursue on a large scale in the near future. One is to combine fossil fuel-based hydrogen production with carbon capture and storage. The second is to use water electrolysis powered by electricity from low-carbon sources, such as renewable energy or nuclear power.
Click here to see data from the infographic above in a table.
| Type of hydrogen | Description | Could it be a climate solution? |
|---|---|---|
| Black hydrogen | Black hydrogen is made by gasifying anthracite (or "black") coal. | No |
| Brown hydrogen | Black hydrogen is made by gasifying lignite (or "brown") coal. | No |
| Gray hydrogen | The majority of hydrogen produced today is gray hydrogen, made from methane gas (CH4) through a process called “steam reforming” that separates the methane’s hydrogen from its carbon. Methane itself is a strong climate-warming greenhouse gas, and the process also creates climate-warming carbon dioxide (CO2). | No |
| Blue hydrogen | Blue hydrogen, like gray hydrogen, uses steam reforming of methane gas, but adds a “carbon capture” step to separate the resulting CO2, compress it into a fluid, and pump it underground. | Yes, if it is successful enough at controlling both methane and CO2 emissions |
| Turquoise hydrogen | Turquoise hydrogen uses “pyrolysis,” raising methane gas to such a high temperature that the carbon in it becomes a solid. | Yes, if it is successful enough at controlling methane emissions |
| Green hydrogen | Through “electrolysis,” electricity can be used to split water (H2O) into hydrogen and oxygen. If that electricity comes from a clean energy source, the process makes almost no climate pollution at all. Green hydrogen uses clean renewable energy like wind, solar or hydropower. | Yes |
| Pink hydrogen | Pink hydrogen, like green hydrogen, uses electrolysis of water, but the electricity is supplied with clean nuclear power. | Yes |
| White hydrogen | In some rare cases, hydrogen can form naturally underground. Until recently, this white hydrogen was thought to be so rare it could not be used as a fuel at any serious scale, but new discoveries beginning in the late 2010s have led multiple companies to explore tapping underground hydrogen stores—or even recreating the conditions that form natural hydrogen deposits. | Yes |
Breathing new life into an old idea
Hydrogen has been in the public imagination since the 1870s, when Jules Verne wrote that “water will be the coal of the future” in his novel The Mysterious Island. However, interest in hydrogen has changed over time. The idea of a “hydrogen economy” was first introduced in the 1970s, to describe using hydrogen as a fuel for the transportation sector at a time when oil prices were rising quickly. Now, the attraction of the hydrogen economy is as a tool for fighting climate change, by replacing fossil fuels in some of the hardest parts of our economy to decarbonize. A key barrier that needs to be overcome to support this transition is the lack of hydrogen infrastructure such as hydrogen pipeline networks, widespread production facilities, and hydrogen fueling stations.
Updated July 25, 2025.
1 International Energy Agency: Hydrogen. Updated February 27, 2025.







